Quick definition: IoT security is the combination of technologies and processes that businesses use to protect their connected devices from cyberattacks.
Any Internet-enabled device is vulnerable to being hacked and misused. In the age of the Internet of Things, there are billions of connected devices someone could use to access private data, spread malware, or even cause tangible harm.
As government agencies, businesses, and consumers use and rely on a growing number of IoT applications, IoT network security will continue to be a crucial consideration for manufacturers and end users alike. And while some of the burden of IoT security falls on the end user’s shoulders, manufacturers need to build-in security precautions as well. It’s a shared responsibility.
Cybersecurity is continually evolving. And if you want to protect your organization and your end users from the attacks that target IoT devices, you need to be familiar with:
- The most prevalent IoT security risks
- Lessons from famous IoT security breaches
- Modern IoT security solutions
With the right technologies, design, and maintenance, you can be confident in your IoT application’s security—whether you’re building smart cars, baby monitors, pacemakers, tracking devices, farm equipment, or something no one’s ever seen before.
We’re going to get into some of the infrastructure and technology decisions that help keep your application secure, but first, let’s look at the inherent vulnerabilities with IoT devices.
IoT security risks
Internet-enabled devices pose a number of security challenges. But while the Internet of Things has brought connectivity to new devices, the general cybersecurity issues aren’t really new. We’ve been dealing with hackers for as long as we’ve enjoyed the benefits of the Internet.
Weak authentication
Passwords are one of the first lines of defense against hacking attempts. But if your password isn’t strong, your device isn’t secure. Most default passwords are relatively weak—because they’re intended to be changed—and in some cases they may be publicly accessible or stored in the application’s source code. (That’s extremely risky.)
End users may also set the password to something that’s easy to remember. But if it’s easy to remember, it’s probably easy to penetrate.
Many IoT devices have little or no authentication at all. Even if there’s no important data stored on the device itself, a vulnerable IoT device can be a gateway to an entire network, or it can be assimilated into a botnet, where hackers can use its processing power to distribute malware and distributed denial of service (DDoS) attacks.
Weak authentication is a serious IoT security concern. Manufacturers can help make authentication more secure by requiring multiple steps, using strong default passwords, and setting parameters that lead to secure user-generated passwords.
Low processing power
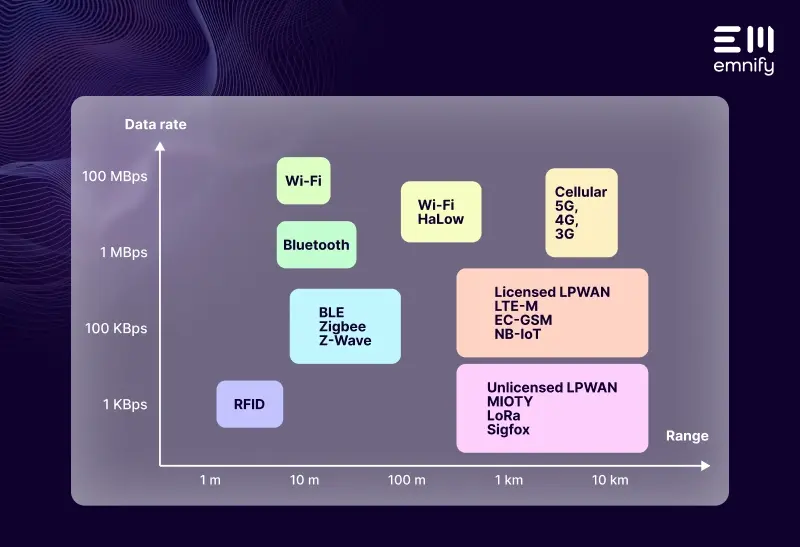
Most IoT applications use very little data. This reduces costs and extends battery life, but it can make them difficult to update Over-the-Air (OTA), and prevents the device from using cybersecurity features like firewalls, virus scanners, and end-to-end encryption. This ultimately leaves them more vulnerable to hacking.
This is where it’s crucial that the network itself has built-in security features.
Legacy assets
If an application wasn’t originally designed for cloud connectivity, it’s probably ill-equipped to combat modern cyber attacks. For example, these older assets may not be compatible with newer encryption standards. It’s risky to make outdated applications Internet-enabled without making significant changes—but that’s not always possible with legacy assets. They’ve been cobbled together over years (possibly even decades), which turns even small security improvements into a monumental undertaking.
Shared network access
It’s easier for IoT device to use the same network as the end user’s other devices—such as their WiFi or LAN—but it also makes the entire network more vulnerable. Someone can hack an IoT device to get their foot in the door and gain access to more sensitive data stored on the network or other connected devices. Likewise, another device on the network could be used to hack the IoT device. In either of those scenarios, customers and manufacturers wind up pointing fingers at each other.
Every IoT application should use a separate network and/or have a security gateway or firewall—so if there’s a security breach on the device, it remains isolated to the device. (This is one of the advantages of cellular IoT.) A Virtual Private Network (VPN) helps protect your devices from outside the network, but if your application shares a connection with other devices, it’s still vulnerable to attacks from them if they become corrupted.
Inconsistent security standards
Within IoT, there’s a bit of a free-for-all when it comes to security standards. There’s no universal, industry-wide standard, which means companies and niches all have to develop their own protocols and guidelines. The lack of standardization makes it harder to secure IoT devices, and it also makes it harder to enable machine-to-machine (M2M) communication without increasing risk.
Lack of encryption
One of the greatest threats to IoT security is the lack of encryption on regular transmissions. Many IoT devices don’t encrypt the data they send, which means if someone penetrates the network, they can intercept credentials and other important information transmitted to and from the device.
Missing firmware updates
Another of the biggest IoT security risks is if devices go out in the field with a bug that creates vulnerabilities. Whether they come from your own developed code or a third party, manufacturers need the ability to issue firmware updates to eliminate these security risks. Ideally, this should happen remotely, but that’s not always feasible. If a network’s data transfer rates are too low or it has limited messaging capabilities, you may have to physically access the device to issue the update.
Gaps between mobile networks and the cloud
Many IoT devices regularly interact with cloud-based applications. And while the cellular network an IoT device uses may be secure, and the cloud application may be secure, transmissions from the network to the cloud typically pass through the public Internet, leaving them vulnerable to interception and malware. Even these small gaps can compromise an entire IoT deployment. Thankfully, IoT manufacturers and their customers can close them with cloud-based connectivity solutions.
Limited device management
Businesses often lack the visibility and control they need to see when a device has been compromised and then deactivate it. Every Mobile Network Operator (MNO) has their own connectivity management platform, and some give customers very little insight or functionality. Hacked or compromised devices tend to consume data differently, and so end users should be able to detect anomalous behavior and remotely deactivate these devices before they have opportunities to cause greater harm.
Physical vulnerabilities
Not all IoT devices operate in remote areas. Some regularly come into contact with people, which opens the door to unauthorized access. In fleet management, for example, it’s not uncommon for drivers to steal SIM cards from their vehicle’s GPS trackers to use them for “free data.” Other thieves may steal SIM cards to commit identity theft. People can also physically access IoT devices for more nefarious purposes, like accessing a network or stealing information.
End users can’t always watch their IoT devices to ensure no one is physically accessing them, so it’s important to consider ways to harden devices with better components and security features.
Examples of IoT security breaches
Especially in recent years, there have been numerous examples of how even innocuous IoT devices can be abused and repurposed to cause harm. Some of the more famous examples have merely been revelations of what’s possible, but others have involved actual attacks.
Here are just a few examples of IoT security breaches.
Mirai botnet
The 2016 Mirai botnet is one of the more infamous IoT security breaches, in part because it was the largest attack we’ve seen so far, but also because the code is still out there. The original hacker posted the code online, opening the door to copycats.
A botnet is essentially a distributed network of computers. They’re not inherently bad, but in the wrong hands, a botnet is an army of devices that can take down servers. In Mirai’s case, the botnet consisted of 145,607 video recorders and IP cameras. The hacker (a college student) launched an unprecedented attack on OVH (a French web hosting service), using the botnet to take up nearly one terabyte of bandwidth per second.
The botnet was made possible by unsecured IoT devices. The objective of the first attack was surprisingly insignificant: crashing some Minecraft servers. But about a month later, the Mirai botnet targeted another service provider: Dyn. And that time, Mirai brought down huge sections of the Internet, including Netflix, Twitter, Reddit, The Guardian, and CNN.
Mirai’s model is still in use, and other hackers are bound to have more nefarious goals if they can get their hands on that many vulnerable Internet-enabled devices.
Target’s credit card breach
In 2013, hackers successfully breached Target’s network and stole credit card information from millions of transactions. How’d they do it? They stole login credentials from an HVAC vendor, who was using IoT sensors to help Target monitor their energy consumption and make their systems more efficient.
While an IoT device may not be at fault here, the implications should be clear to anyone manufacturing IoT applications, particularly applications like smart meters. People may attempt to hack your network in order to access a client’s network. At any given moment, your devices may only be a couple steps removed from extremely valuable (and private) data, even if it has nothing to do with your application.
St. Jude Medical’s pacemakers
In 2017, the FDA announced that more than 465,000 implantable pacemaker devices were vulnerable to hacking. While there were no known hacks, and St. Jude Medical quickly updated the devices to fix their security flaws, it was a disturbing revelation with deadly implications.
With control of one of these devices, a hacker could literally kill someone by depleting the battery, altering someone’s heart rate, or administering shocks.An IoT security flaw essentially turned a life-saving device into a potentially deadly weapon.
Hackable vehicles
In 2015, a pair of cybersecurity experts set out to hack a brand new Jeep Grand Cherokee using its multimedia system. They were successful. And they demonstrated that they could use the multimedia system to connect to another piece of software in the vehicle, reprogram it, and then control the engine, steering wheel, brakes, transmission, and more.
They effectively turned the Jeep Grand Cherokee into a lifesize remote control car.
In the age of self-driving cars, this demonstration is a haunting reminder that isolating connected devices is a crucial component of IoT security.
IoT security solutions
Security is imperative. For IoT businesses and vendors, the introduction of new technology and the increase in global deployments bring a myriad of new security issues that need to be considered when deploying M2M devices.
1. Physical security
Since IoT applications are often remote, physical security is crucial for preventing unauthorized access to a device. This is where it’s valuable to use resilient components and specialized hardware that makes your data more difficult to access.
For example, in cellular IoT devices, lots of critical information is stored on the SIM card. Most form factors for SIMs are removable, which makes this data more vulnerable. An eSIM, however, is soldered directly onto the circuit board. They’re harder to physically access, and they’re also more resistant to changes in temperature and shock damage, which are sometimes used in attempts to sabotage or hack a device.
2. Remote access security
Moreover, a robust remote-access security protocol is needed that allows
- SIM functionality to be locked to specific devices
- The ability to remotely disable connections if there’s a physical security breach
3. Private networks
Sending and receiving messages through remotely deployed devices is in itself a security risk. Connecting devices and enabling this communication using public-access networks, such as WiFi, opens up those messages for interception.
Encrypting messages is a step in the right direction but using public networks to send sensitive data demands more precautions. We recommend building private networks on top of existing security mechanisms to ensure that data never crosses the public Internet.
emnify helps IoT manufacturers create Virtual Private Networks (VPNs) using OpenVPN, a versatile open standard that gives you secure remote access to your devices from anywhere.
4. Abnormality detection
The moment someone attempts to breach your device or there’s abnormal network activity, you need to know. With a emnify's cloud communication platform, we forward the relevant connectivity information to your operational dashboards, where you can evaluate whether there was an employee error or a serious threat.
5. IMEI lock
An International Mobile Station Equipment Identity (IMEI) is the unique ID number found on most mobile devices. An IMEI lock will enable you to configure a SIMs functionality to a specific IMEI in real time to prevent the SIM being removed and used in any other device.
6. Encrypted data transfer
To securely transport data to and from your devices, you need to encrypt data transfers within the network. There are a variety of protocols developers can use to secure a device’s communication, the most common of which is Transport Layer Security (TLS). But while your application and network may be secure, there’s a gap between them where your data can be intercepted. Using an X.509 certificate and/or a single VPN/IPSec connection between the mobile network and the application server, you can close this security gap.
Alternatively, emnify also enables you to use intra-cloud connect to establish a secure VPN for your entire deployment, so there’s no need for public IPs.
7. Network-based firewall
Typically, small M2M devices have limited processing power. This prevents them from establishing firewalls. A network-based firewall, however, protects your data the moment it enters the network. This takes the labor-intensive process of packet filtering away from the device, ensuring malicious traffic is never transmitted to the device or even able to enter the network in the first place.
Network-based firewalls allow businesses to monitor and block traffic outside of your VPN, or simply block specific communications. It can also detect intrusions or hacking attempts that do not align with pre-configured policies.
8. Limited connectivity profile
Your IoT application was designed for a specific purpose. The more you can isolate your device’s network connectivity to its core functions, the more secure it will be. Does it need access to voice capabilities? Does it need to receive external SMS messages? If not, that functionality should be restricted.
Secure your IoT device
Protecting your IoT device requires a combination of technology and best practices. Holes in your connectivity solution can leave your devices, data, and customers vulnerable to cyber attacks.
While enterprises are responsible for using secure systems to transport business and consumer data, device manufacturers are responsible for providing security at the production level.
At emnify, we specialize in providing secure connectivity and service management for connected devices through VPN/IPsec, intra-cloud connect, and other network-level security features. We also provide embedded SIMs, helping to protect your devices from physical tampering.
Talk to an IoT security expert today. We’ll help you take steps to protect your customers’ data before your devices even leave the factory.
Get in touch with our IoT experts
Discover how emnify can help you grow your business and talk to one of our IoT consultants today!

If you want to understand how emnify customers are using the platform Christian has the insights. With a clear vision to build the most reliable and secure cellular network that can be controlled by IoT businesses Christian is leading the emnify product network team.