
Connectivity that's
secure by default
See, control, and prevent threats ahead of time thanks to security enforced at the network layer, not bolted onto devices afterwards.
The critical risks you face when connecting IoT devices:

-
Public APNs route your traffic across the open internet. This exposes device data to interception, rerouting, and manipulation through insecure paths such as BGP hijacks.
-
You need real time visibility into how your IoT data moves. Without it, unknown IPs, abnormal usage spikes, and unauthorized device behaviour go undetected and become security risks.
-
Cross border connections often send your data through regions with different security and privacy rules. If these routes are unprotected, they can violate local regulations and create compliance exposure.
-
Your SIMs act as network credentials. If they are removed, copied, or used in other devices, attackers can generate unauthorized traffic.
So, how is emnify's connectivity 'secure by default’?
You need security built into your connectivity, not bolted on at the device or application like most traditional operators. emnify makes this possible by leveraging capabilities via our cloud native core that keep every connection protected, visible, and controlled by design.
See everything
You cannot secure what you cannot see.
emnify gives you continuous, real-time visibility into how every device connects, communicates, and behaves across networks and regions.
What visibility you will have
Real time insight into every device and connection
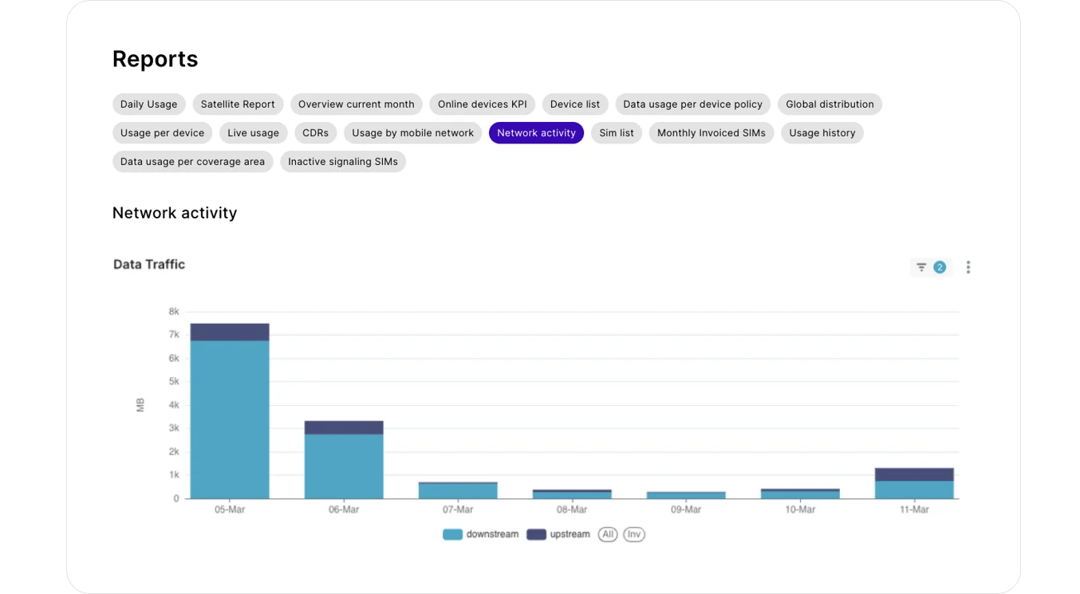
emnify’s Data Streamer delivers live connectivity events and traffic metadata directly into your own systems via API, or into the Events Centre. You see roaming changes, DNS queries, IP endpoints, and traffic activity the moment they happen.
Full visibility of where your traffic goes
With Flow Logs, you get detailed metadata for every device flow, including IP addresses, ports, protocols, byte and packet counts, location, and RAT, so you can identify unusual destinations or abnormal behaviour.
Deep diagnostics when something looks suspicious
Packet Capture gives you full packet payloads for advanced troubleshooting. Use it to analyse protocol behaviour, MTU issues, or security anomalies when you need deep investigation.
Clear insight into DNS activity
Through Flow Logs and Data Streamer, you see exactly which domains your devices query and connect to. This helps you spot unexpected lookups, detect suspicious destinations, and understand backend communication behaviour in real time.
How this helps your operations:
This visibility helps you spot suspicious behaviour immediately, understand where traffic is going, detect unexpected destinations, and investigate issues without relying on operators.
Want to know more about Network Insights?
Control everything
Visibility is only useful if you can act on it.
emnify lets you define and enforce precise rules that govern device behaviour, data paths, and access boundaries across your entire deployment.
How you can do it:
Configure policies that govern what devices can and can’t do
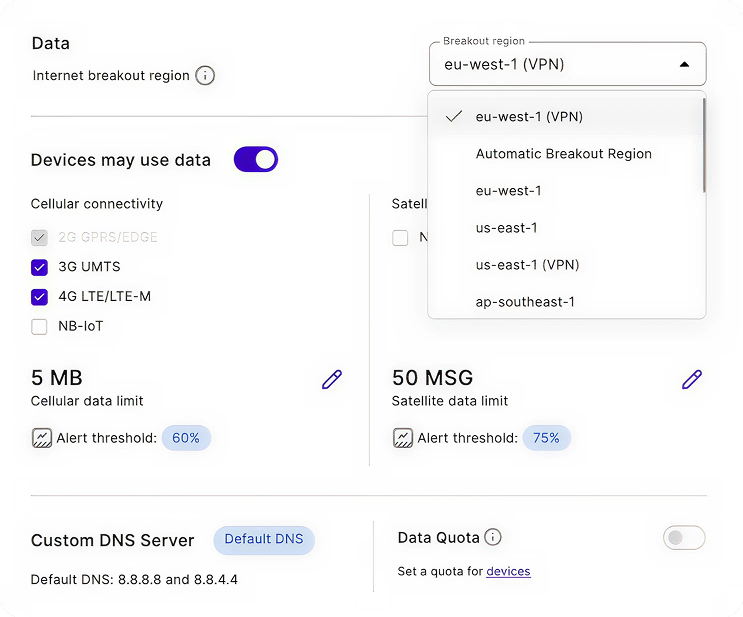
Set precise rules that control which networks a SIM can attach to, which regions it can operate in, and how much data or SMS it can consume.
Control how your data moves
Control the path your device traffic takes after it leaves the network with Cloud Connect. Device data is routed through private, cloud to cloud connections such as IPsec VPN, AWS Transit Gateway, or OpenVPN directly into your environment, instead of traversing the public internet.
Prevent direct access to your devices
With a private IP address space, your devices are never assigned public, internet routable IP addresses. They cannot be scanned, discovered, or accessed directly from the internet, and are only reachable through controlled, private connections you define.
Control which services your devices can communicate with
With DNS Filtering, you can define which domains your devices are allowed to resolve and connect to. This gives you visibility and control over backend communication, helping prevent devices from reaching malicious, unintended, or unauthorised services.
Control who can access and operate your connectivity platform
Use SSO, RBAC, multi-project separation, and audit logs to ensure only authorised users can manage SIMs, routing, and policies, with full traceability across teams.
Ensure SIMs only work in approved hardware
With IMEI Lock, each SIM is bound to a specific device. If a SIM is removed or inserted into different hardware, connection attempts are blocked automatically.
How this secures your operations:
Together, these controls let you strictly govern device behaviour, data paths, and access at every level. They prevent SIM misuse, block unauthorised destinations, reduce attack surface, and ensure connectivity behaves exactly as intended across your deployment.
What is IPsec?
Prevent everything
Security is strongest when attack paths are removed, not just monitored. emnify’s network architecture eliminates common IoT attack vectors and compliance failure modes by design.

How emnify prevents threats to your devices:
Your devices cannot be exposed to the public internet
Devices are never publicly addressable. They cannot be discovered, scanned, or accessed directly from the internet. Inbound attack vectors that rely on public exposure do not exist.
Your data cannot be intercepted in transit
Device traffic never traverses best-effort public internet paths. As a result, interception, BGP hijacks, and passive eavesdropping are structurally impossible.
SIMs cannot be reused or abused in unauthorised hardware
SIM identities are enforced at the network layer. If a SIM is removed, copied, or inserted into different hardware, it will not attach. SIM misuse cannot escalate into a security or compliance incident.
Your data cannot unintentionally leave approved regions
Traffic does not accidentally exit allowed jurisdictions. Data residency violations caused by misrouting or roaming behaviour are structurally prevented.
Incidents cannot spread across your deployment
Each device operates in isolation. There is no lateral movement between devices, and no shared exposure. If a device is compromised, the impact is contained and cannot cascade.
How this secures your operations:
By enforcing security at the network layer, emnify prevents exposure, interception, misuse, and compliance violations before they can occur. Risks are eliminated structurally, not detected after the damage is done, and any compromise is isolated to a single device.
Ready to make security your default?
Join IoT leaders trusting emnify for always connected, always protected deployments. Contact us to discuss how our cloud-native network transforms your IoT security.